*By Kelvin Vasques
*By Kelvin Vasques
There is no turning back on the path to decentralizing IT infrastructures in companies. In recent years, we have seen a significant shift in the enterprise technology environment. The traditional digital approach, characterized by data centers and restricted networks, has largely been replaced by a much more distributed one that even allows for greater scalability of operations. The market is still dealing with the acceleration of the adoption of hybrid work and the growing trend of BYOD (Bring Your Own Device). Given this scenario, we observed an increase in edge security gaps (Edge Security), which processes and analyzes data closest to where it is generated, stored, accessed or transmitted.
As employees began accessing corporate applications and information through often unsecured home networks or personal devices, organizations faced significant cybersecurity challenges at all ends. In this context, investing in cybersecurity has never been more mandatory to protect businesses.
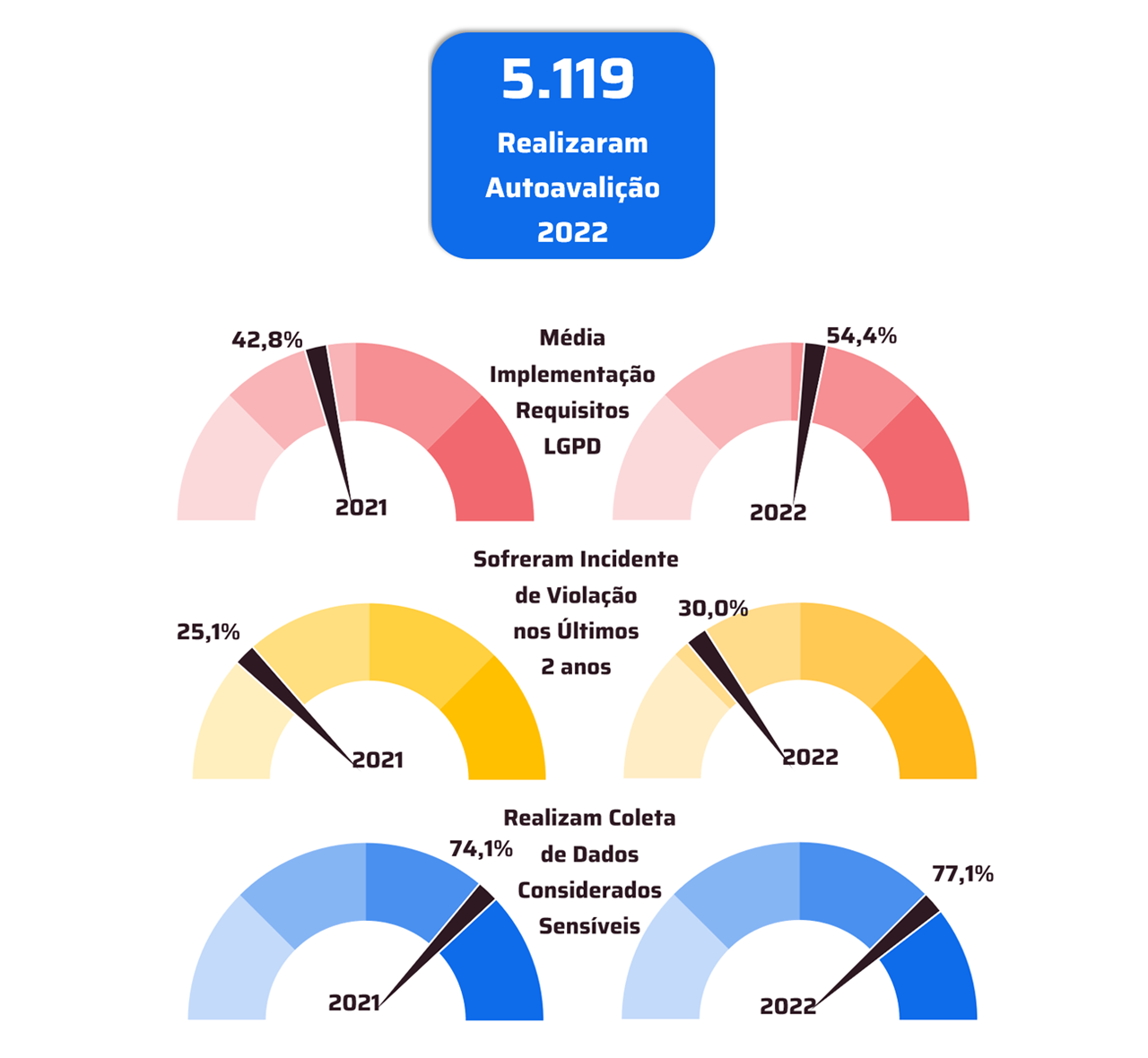
In Brazil, one of the main targets of cybercrimes for years, the increase in sophistication, volume and frequency of attacks has placed cybersecurity focused on protecting endpoints at the center of strategies, with a comprehensive and integrated approach. The more distributed IT resources are across a variety of environments, networks, devices and platforms, the more the attack surface is expanded, making security margins less defined. Furthermore, distributed infrastructures are more complex to manage, and the lack of complete visibility over all the assets contained therein can make early detection of malicious activity difficult, even impacting compliance with standards, security regulations and data protection law. , such as the General Personal Data Protection Law (LGPD), Payment Card Industry Data Security Standard (PCI), National Institute of Standards and Technology (NIST), among others.
Even though the necessary technologies are available to deal with these challenges, many companies believe that it is necessary to make large investments, in financial resources or in time for implementation, to keep their data protected. There is also a belief in the market that existing innovations are only aimed at businesses that have already reached maturity with regard to digitalization. However, these ideas need to be demystified. Several accessible measures to protect information and, consequently, operations, are available even for companies in the early stages of this journey.
By adopting a Next-Generation Firewall, for example, companies already receive broad protection against various threats. These solutions are capable of offering multi-layer defense at all points of entry into the network, regardless of the size or complexity of the operation. To achieve this, the technology combines broad intrusion detection and prevention capabilities, protection against advanced malware threats, secure connectivity channels, communication and remote access, and control policies with deep traffic inspection. Furthermore, it makes it possible to define which sites, categories or applications can be accessed using web content filters to mitigate risks. If any threat leaves the devices, it will be blocked before reaching the company's internal network.
For organizations with high-risk operations, such as hospitals, healthcare clinics, e-commerce retailers or large legal and accounting firms, the adoption of a Next-Generation Firewall and technologies such as SD-WAN (Software-Defined WAN) can significantly increase security and availability by creating a higher performance network for communication and access to data and applications. SD-WAN allows the use of different connectivity and communication links, whether public or private, to connect numerous branches to their headquarters and remote users to the business environment, supporting the creation of an IT infrastructure with greater performance and flexibility and resilience. Based on encryption, the technology guarantees the confidentiality of transmitted information, preventing unauthorized people from accessing it. SD-WAN networks also provide mechanisms for content filtering, access control, intrusion prevention, and protection against attacks and threats such as DDoS, Port Scanning, and others.
Currently, cybersecurity should be on the discussion agenda of all sectors. On a business protection journey, it is important that companies do not see Edge Security as just another cost. It is, indeed, an essential investment, especially when we think about the invaluable value of data to businesses, which cannot be accessed improperly. For this reason, adopting economically viable security measures, aligned with organizational strategies, guarantees the financial sustainability of the initiative. Combined with employee education and awareness to promote a culture of innovation aligned with cybersecurity, the technologies available today take business reliability to a new level.
Critical sectors such as e-commerce, healthcare and finance are aware of this and prioritize investments in this area. Now, it is necessary for companies in other sectors, large or small, to also rush to adapt. Taking a proactive, integrated approach to protecting endpoints is critically important for mitigating cyber risks and protecting organizations' digital assets. And, as we have seen with the increase in attacks in the country, it is no longer possible to wait to protect yourself, starting with taking care of your Edge Security.
* Kelvin Vasques, Quality Assurance Manager at Blockbit
Notice: The opinion presented in this article is the responsibility of its author and not of ABES - Brazilian Association of Software Companies